“Smishing” (SMS phishing) technology has reached a new, highly dangerous level. Toronto police announced the arrest of three individuals involved in operation “Project Lighthouse” – the first attack of its kind detected in Canadian history. The criminals drove around the city center with advanced interception devices, known as “SMS blasters,” hidden in the back of their cars.
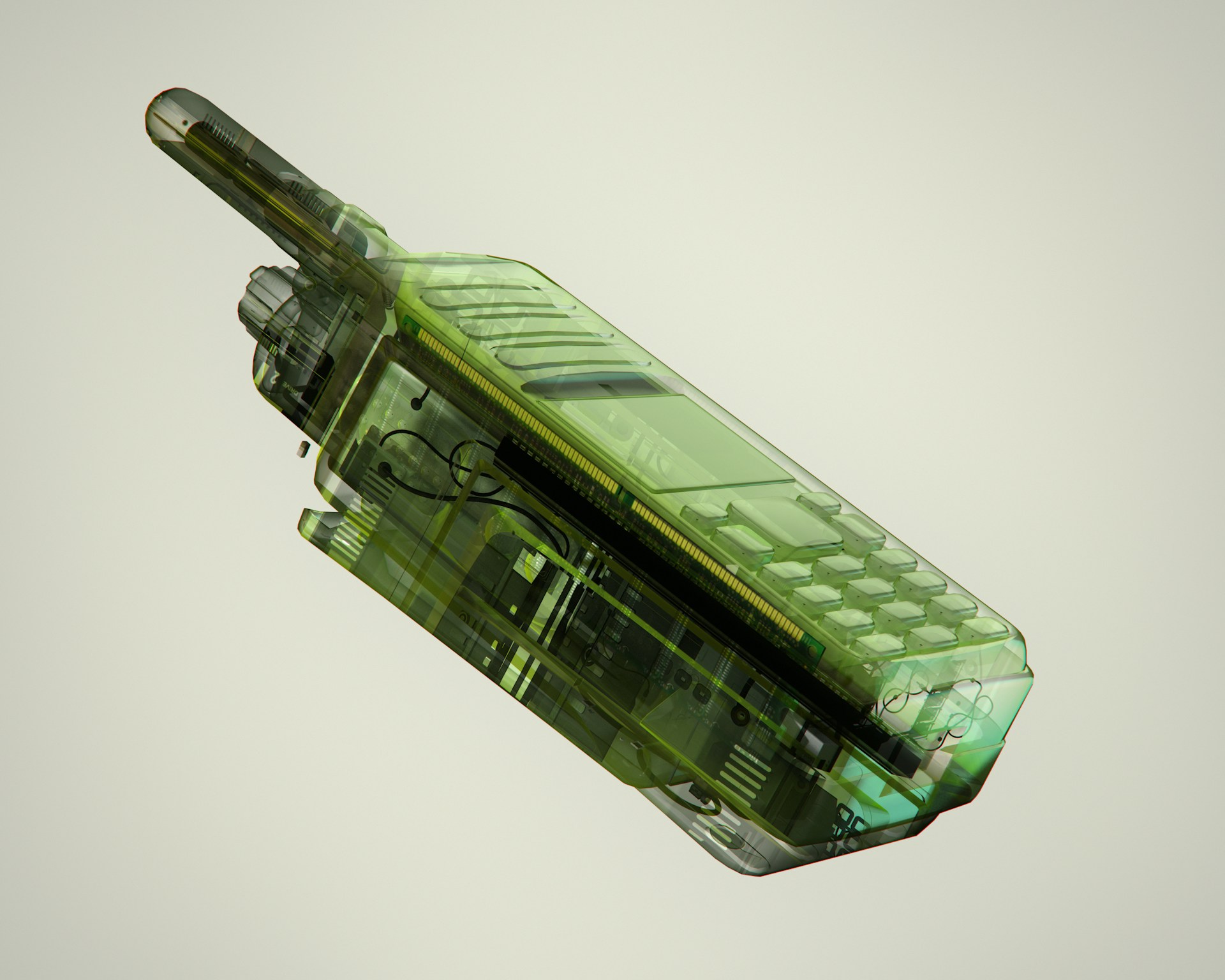
These devices work by simulating legitimate base stations (cell towers). Because they are close to the users – often in a passing car on the street – they offer a stronger signal, causing the victims’ phones to automatically disconnect from the real network and connect to the criminals’ device. This allows the attackers to directly send fake text messages that appear on the phone screen as official communications from banks or government institutions (with a hidden sender number).
The problem is that the attackers weren’t just stealing data. It’s more about that they were physically paralyzing communications. According to investigators, systems registered a staggering 13 million network disruptions, and tens of thousands of devices were trapped by the fake base station. As a result, users were locked out, losing access to legitimate cellular networks, including the ability to call 911 for help.
Robert Johnson, Deputy Chief of the Toronto Police Service, emphasized the severity of the situation during an official press conference:
What makes this particularly concerning is the scale and impact. This wasn’t targeting a single individual or business. It had the ability to reach thousands of devices at once. And beyond the financial risk, there are real public safety implications. For instance, when devices are diverted from legitimate networks, even briefly, it interferes with a person’s ability to connect to emergency services.
For security reasons, Canadian authorities refused to release photos of the seized equipment, emphasizing that the confiscated devices were “uniquely built” by the criminals.
Although this is the first such operation detected in Canada, the phenomenon of mobile “rogue base stations” is growing worldwide, including in the context of terrorism and espionage. In early 2024, Philippine authorities arrested two Chinese nationals who, using similar equipment (IMSI catchers), drove around key government installations, military bases, and the US Embassy in Manila. Such devices can be used not only to spread malicious links but also to directly intercept and record classified voice conversations.